Next-Generation Secure Computing Base: Difference between revisions
(Added new "criticism" section, expanded development history, and fixed minor inconsistencies in the article.) |
m (→Development: Added source for the claim about NGSCB's relation to Microsoft's DRM-OS patents) |
||
| Line 9: | Line 9: | ||
Development of the NGSCB began in 1997 after Microsoft developer, Peter Biddle, conceived of new ways to offer content protection on personal computers.<ref>Schoen, Seth (July 5, 2002). [https://web.archive.org/web/20020802145913/http://vitanuova.loyalty.org/2002-07-05.html "'Palladium' summary"]</ref> | Development of the NGSCB began in 1997 after Microsoft developer, Peter Biddle, conceived of new ways to offer content protection on personal computers.<ref>Schoen, Seth (July 5, 2002). [https://web.archive.org/web/20020802145913/http://vitanuova.loyalty.org/2002-07-05.html "'Palladium' summary"]</ref> | ||
Microsoft later filed a large number of patents related to elements of the NGSCB design. Patents for a digital rights management operating system,<ref>[http://www.google.com/patents/US6330670 Digital rights management operating system (U.S. 6330670 B1)]</ref> loading and identifying a digital rights management operating system,<ref>[http://www.google.com/patents/US6327652 Loading and identifying a digital rights management operating system (U.S. 6327652 B1)]</ref> key-based secure storage,<ref>[http://www.google.com/patents/US7194092 Key-based secure storage (U.S. 7194092 B1)]</ref> and certificate based access control<ref>[http://www.google.com/patents/US6820063 Controlling access to content based on certificates and access predicates (U.S. 6820063 B1)]</ref> were filed on January 8, 1999. A method to authenticate an operating system based on its central processing unit was filed on March 10, 1999.<ref>[http://www.google.com/patents/US7174457 System and method for authenticating an operating system to a central processing unit (U.S. 7174457 B1)]</ref> Patents related to the secure execution of code<ref>[http://www.google.com/patents/US6651171 Secure execution of program code (U.S. 6651171 B1)]</ref> and protection of code in memory<ref>[http://www.google.com/patents/US6775779 Hierarchical trusted code for content protection in computers (U.S. 20040243836 A1)]</ref> were filed on April 6, 1999. | Microsoft later filed a large number of patents related to elements of the NGSCB design.<ref>Lampson, Butler [http://research.microsoft.com/en-us/um/people/blampson/cv.doc "Curriculum Vitae"]</ref> Patents for a digital rights management operating system,<ref>[http://www.google.com/patents/US6330670 Digital rights management operating system (U.S. 6330670 B1)]</ref> loading and identifying a digital rights management operating system,<ref>[http://www.google.com/patents/US6327652 Loading and identifying a digital rights management operating system (U.S. 6327652 B1)]</ref> key-based secure storage,<ref>[http://www.google.com/patents/US7194092 Key-based secure storage (U.S. 7194092 B1)]</ref> and certificate based access control<ref>[http://www.google.com/patents/US6820063 Controlling access to content based on certificates and access predicates (U.S. 6820063 B1)]</ref> were filed on January 8, 1999. A method to authenticate an operating system based on its central processing unit was filed on March 10, 1999.<ref>[http://www.google.com/patents/US7174457 System and method for authenticating an operating system to a central processing unit (U.S. 7174457 B1)]</ref> Patents related to the secure execution of code<ref>[http://www.google.com/patents/US6651171 Secure execution of program code (U.S. 6651171 B1)]</ref> and protection of code in memory<ref>[http://www.google.com/patents/US6775779 Hierarchical trusted code for content protection in computers (U.S. 20040243836 A1)]</ref> were filed on April 6, 1999. | ||
Microsoft publicly demonstrated the NGSCB for the first time at its Windows Hardware Engineering Conference in 2003.<ref>Bekker, Scott (May 6, 2003). [http://redmondmag.com/articles/2003/05/06/palladium-on-display-at-winhec.aspx "'Palladium' on Display at WinHEC"]</ref><ref>BusinessWire (May 7, 2003). [http://www.businesswire.com/news/home/20030507005219/en/Atmel-Microsoft-Demonstrate-Secure-USB-Keyboard-Prototype "Atmel and Microsoft Demonstrate New Secure USB Keyboard Prototype at WinHEC 2003"]</ref><ref> Microsoft PressPass: [http://www.microsoft.com/en-us/news/features/2003/may03/05-07ngscb.aspx "At WinHEC, Microsoft Discusses Details of Next-Generation Secure Computing Base"]</ref> | Microsoft publicly demonstrated the NGSCB for the first time at its Windows Hardware Engineering Conference in 2003.<ref>Bekker, Scott (May 6, 2003). [http://redmondmag.com/articles/2003/05/06/palladium-on-display-at-winhec.aspx "'Palladium' on Display at WinHEC"]</ref><ref>BusinessWire (May 7, 2003). [http://www.businesswire.com/news/home/20030507005219/en/Atmel-Microsoft-Demonstrate-Secure-USB-Keyboard-Prototype "Atmel and Microsoft Demonstrate New Secure USB Keyboard Prototype at WinHEC 2003"]</ref><ref> Microsoft PressPass: [http://www.microsoft.com/en-us/news/features/2003/may03/05-07ngscb.aspx "At WinHEC, Microsoft Discusses Details of Next-Generation Secure Computing Base"]</ref> | ||
Revision as of 23:28, 26 June 2014
The Next-Generation Secure Computing Base (codenamed Palladium) is the name of a cancelled software architecture originally slated to be included in the Microsoft Windows "Longhorn" operating system. Development of the architecture began in 1997.[1][2]
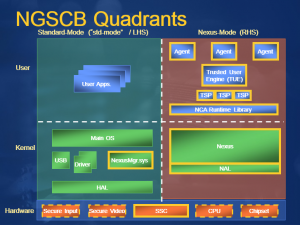
NGSCB is designed to provide an isolated environment where sensitive operations may be performed securely. Microsoft's primary stated objective with NGSCB is to "protect software from software."[3]
History
Development
Development of the NGSCB began in 1997 after Microsoft developer, Peter Biddle, conceived of new ways to offer content protection on personal computers.[4]
Microsoft later filed a large number of patents related to elements of the NGSCB design.[5] Patents for a digital rights management operating system,[6] loading and identifying a digital rights management operating system,[7] key-based secure storage,[8] and certificate based access control[9] were filed on January 8, 1999. A method to authenticate an operating system based on its central processing unit was filed on March 10, 1999.[10] Patents related to the secure execution of code[11] and protection of code in memory[12] were filed on April 6, 1999.
Microsoft publicly demonstrated the NGSCB for the first time at its Windows Hardware Engineering Conference in 2003.[13][14][15]
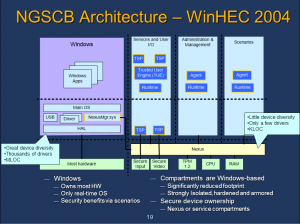
At WinHEC 2004, Microsoft announced that it would reconsider its plans for the platform, based on feedback from customers and ISV partners who stated that they did not want to rewrite their existing programs in order to benefit from its functionality.[16][17] Although some reports stated that Microsoft planned to cancel the platform because of this,[18][19] Microsoft reaffirmed its commitment to the technology.[20][21]
Name
In Greek and Roman mythology, the term "palladium" refers to an object that the safety of a city or nation was believed to be dependent upon.[22]
On January 24, 2003, Microsoft announced that "Palladium" had been renamed as the "Next-Generation Secure Computing Base." According to NGSCB product manager Mario Juarez, the new name was chosen not only to reflect Microsoft's commitment to the technology in the upcoming decade, but also to avoid any legal conflict with an unnamed company that had already acquired the rights to the Palladium name. Juarez acknowledged that the previous name had been a source of controversy, but denied that the decision was made by Microsoft in an attempt to deflect attention.[23]
Criticism
Cancellation
At WinHEC 2005, Microsoft announced that its plans had been scaled back in order to ship the post-reset Windows "Longhorn" operating system within a reasonable timeframe. Instead of providing a new operating environment, the NGSCB would offer full volume encryption with a feature known as "Secure Startup" (later renamed as "Bitlocker Drive Encryption").[24] Microsoft stated that it would deliver other aspects of its NGSCB vision at a later date.[25]
In July 2008, Peter Biddle stated that negative perception was the main factor responsible for the cancellation of the architecture.[26]
Overview and features
Process isolation
Sealed storage
Attestation
Attestation refers to validation of a NGSCB machine configuration. Attestation allows users to attest to the state of a hardware or software configuration by sending its cryptographic information to a trusted third-party; the third-party can then determine whether it should trust the configuration.
Secure I/O
Software
Nexus
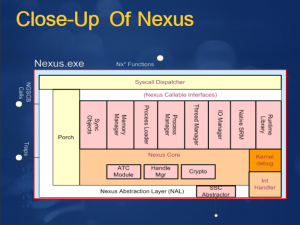
The Nexus, previously referred to as the "Nub"[27] or "Trusted Operating Root"[28][29] is the security kernel in the NGSCB software platform. The Nexus is responsible for the secure interaction between the specialized hardware components, and is also responsible for the management of Nexus Computing Agents.
Nexus Computing Agents
Nexus Computing Agents are user-mode application processes managed by the Nexus kernel.
Nexus Computing Agents are divided into three categories: "Application," "Component," and "Trusted Service Provider."[30]
Hardware
Trusted Platform Module
The Trusted Platform Module, previously referred to as the "Secure Cryptographic Processor" or "Security Support Component", is the hardware component that securely stores the cryptographic keys for the Nexus and Nexus Computing Agents, which makes the sealed storage and attestation features of the Nexus possible.
The Trusted Platform Module includes an asymmetric 2048-bit RSA key pair, referred to as the Endorsement Key (EK), which is unique to each particular module and is generated as part of its manufacturing process. The public key is accessible to applications or services that have established a trusted relationship with the owner, and is also used to provide the owner with Attestation Identity Keys (AIKs).
According to Microsoft, version 1.2 of the Trusted Platform Module is the first version compatible with its NGSCB architecture. Previous versions do not include the required functionality.[31]
In builds of Windows "Longhorn"
In released pre-reset builds of Windows "Longhorn", NGSCB components reside in %SYSTEMDRIVE%\WINDOWS\NGSCB.
In Windows 8
On systems equipped with a Trusted Platform Module, Windows 8 incorporates a feature called "Measured Boot" which allows a trusted server to verify the integrity of the Windows startup process.[32][33][34] Measured Boot is not directly related to the NGSCB architecture; rather, it serves a purpose comparable to the architecture's "Attestation" feature in that both are designed to validate a platform configuration.[35]
References
- ↑ Biddle, Peter (August 5, 2002). "Re: Dangers of TCPA/Palladium"
- ↑ Merritt, Rick (July 15, 2002). "Microsoft scheme for PC security faces flak"
- ↑ Aday, Michael "Palladium"
- ↑ Schoen, Seth (July 5, 2002). "'Palladium' summary"
- ↑ Lampson, Butler "Curriculum Vitae"
- ↑ Digital rights management operating system (U.S. 6330670 B1)
- ↑ Loading and identifying a digital rights management operating system (U.S. 6327652 B1)
- ↑ Key-based secure storage (U.S. 7194092 B1)
- ↑ Controlling access to content based on certificates and access predicates (U.S. 6820063 B1)
- ↑ System and method for authenticating an operating system to a central processing unit (U.S. 7174457 B1)
- ↑ Secure execution of program code (U.S. 6651171 B1)
- ↑ Hierarchical trusted code for content protection in computers (U.S. 20040243836 A1)
- ↑ Bekker, Scott (May 6, 2003). "'Palladium' on Display at WinHEC"
- ↑ BusinessWire (May 7, 2003). "Atmel and Microsoft Demonstrate New Secure USB Keyboard Prototype at WinHEC 2003"
- ↑ Microsoft PressPass: "At WinHEC, Microsoft Discusses Details of Next-Generation Secure Computing Base"
- ↑ Evers, Joris (May 5, 2004). "WinHEC: Microsoft revisits NGSCB security plan"
- ↑ Sanders, Tom (May 6, 2004) "Microsoft shakes up 'Longhorn' security"
- ↑ Bangeman, Eric (May 5, 2004). "Microsoft kills Next-Generation Secure Computing Base"
- ↑ Rooney, Paula (May 5, 2004). "Microsoft shelves NGSCB project as NX moves to center stage"
- ↑ eWeek (May 5, 2004). "Microsoft: Palladium is still alive and kicking"
- ↑ Thurrott, Paul (May 7, 2004). "WinHEC 2004 Show Report and Photo Gallery"
- ↑ Greek Mythology Index: "PALLADIUM"
- ↑ Lemos, Robert (January 24, 2003). "What's in a name? Not Palladium"
- ↑ Sanders, Tom (April 26, 2005). "'Longhorn' security gets its teeth kicked out"
- ↑ Microsoft Next-Generation Secure Computing Base
- ↑ Biddle, Peter (July 16, 2008). "Perception (or, Linus gets away with being honest again)"
- ↑ Biddle, Peter (August 5, 2002). "Re: Dangers of TCPA/Palladium"
- ↑ Microsoft: "'Palladium': A Business Overview"
- ↑ Biddle, Peter (September 19, 2002). "Re: Cryptogram: 'Palladium' only for DRM"
- ↑ Cram, Ellen (October 2003). "Development Considerations for Nexus Computing Agents"
- ↑ Microsoft: "Privacy-Enabling Enhancements in the Next-Generation Secure Computing Base"
- ↑ Microsoft TechNet: "Windows 8 Boot Process - Security, UEFI, TPM"
- ↑ Microsoft TechNet: "Windows 8 Boot Security FAQ"
- ↑ Microsoft Software Developer Network: "Measured Boot"
- ↑ Microsoft: "Secured Boot and Measured Boot: Hardening Early Boot Components against Malware"
External links
Microsoft Next-Generation Secure Computing Base Home Page
| The following article is a stub. You can help BetaArchive Wiki by expanding it. |