Next-Generation Secure Computing Base: Difference between revisions
m (Rewrote "Longhorn" NGSCB directory in uppercase letters for readability and consistency) |
(Added information about Measured Boot in Windows 8. In NGSCB, Attestation could also authenticate configurations not related to the Windows startup process.) |
||
| Line 6: | Line 6: | ||
==In Windows "Longhorn"== | ==In Windows "Longhorn"== | ||
In Windows "Longhorn", components belonging to the NGSCB reside in %SYSTEMDRIVE%\WINDOWS\NGSCB. | In Windows "Longhorn", components belonging to the NGSCB reside in %SYSTEMDRIVE%\WINDOWS\NGSCB. | ||
==In Windows 8== | |||
On systems equipped with a Trusted Platform Module, Windows 8 incorporates a feature called ''Measured Boot'' which allows a trusted server to verify the integrity of the Windows startup process.<ref>Microsoft TechNet: [http://technet.microsoft.com/en-us/windows/dn168167.aspx "Windows 8 Boot Process - Security, UEFI, TPM"]</ref><ref>Microsoft TechNet: [http://technet.microsoft.com/en-us/windows/dn168169.aspx Windows 8 Boot Security FAQ]</ref><ref>Microsoft Software Developer Network: [http://msdn.microsoft.com/en-us/library/windows/desktop/hh848050(v=vs.85).aspx "Measured Boot"]</ref> Measured Boot is not directly related to the NGSCB architecture; rather, it serves a purpose comparable to the architecture's ''Attestation'' feature in that both are designed to verify the integrity of a platform's configuration.<ref>Microsoft: [http://download.microsoft.com/download/4/0/D/40DF6E51-DAD0-4CF8-B768-8E3B4A848D9C/secured-boot-measured-boot.docx "Secured Boot and Measured Boot: Hardening Early Boot Components against Malware"]</ref> | |||
==References== | ==References== | ||
Revision as of 21:25, 9 May 2014
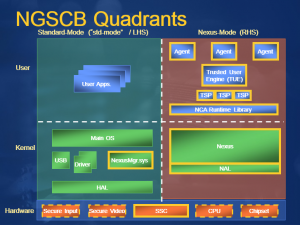
The Next-Generation Secure Computing Base (codenamed Palladium) is the name of a cancelled software architecture originally slated to be included in the Microsoft Windows "Longhorn" operating system. Development of the architecture began in 1997.[1][2]
NGSCB is designed to provide an isolated environment where sensitive operations may be performed securely. Microsoft's primary stated objective with NGSCB is to "protect software from software."[3]
In Windows "Longhorn"
In Windows "Longhorn", components belonging to the NGSCB reside in %SYSTEMDRIVE%\WINDOWS\NGSCB.
In Windows 8
On systems equipped with a Trusted Platform Module, Windows 8 incorporates a feature called Measured Boot which allows a trusted server to verify the integrity of the Windows startup process.[4][5][6] Measured Boot is not directly related to the NGSCB architecture; rather, it serves a purpose comparable to the architecture's Attestation feature in that both are designed to verify the integrity of a platform's configuration.[7]
References
- ↑ Biddle, Peter (August 5, 2002). "Re: Dangers of TCPA/Palladium"
- ↑ Merritt, Rick (July 15, 2002). "Microsoft scheme for PC security faces flak"
- ↑ Aday, Michael. "Palladium"
- ↑ Microsoft TechNet: "Windows 8 Boot Process - Security, UEFI, TPM"
- ↑ Microsoft TechNet: Windows 8 Boot Security FAQ
- ↑ Microsoft Software Developer Network: "Measured Boot"
- ↑ Microsoft: "Secured Boot and Measured Boot: Hardening Early Boot Components against Malware"
| The following article is a stub. You can help BetaArchive Wiki by expanding it. |